Merge branch '42751-rename-mr-maintainer-push' into 'master'
Rephrase Merge Request Maintainer Edit See merge request gitlab-org/gitlab-ce!19061
Showing
38.6 KB
48.1 KB
Rephrase Merge Request Maintainer Edit See merge request gitlab-org/gitlab-ce!19061
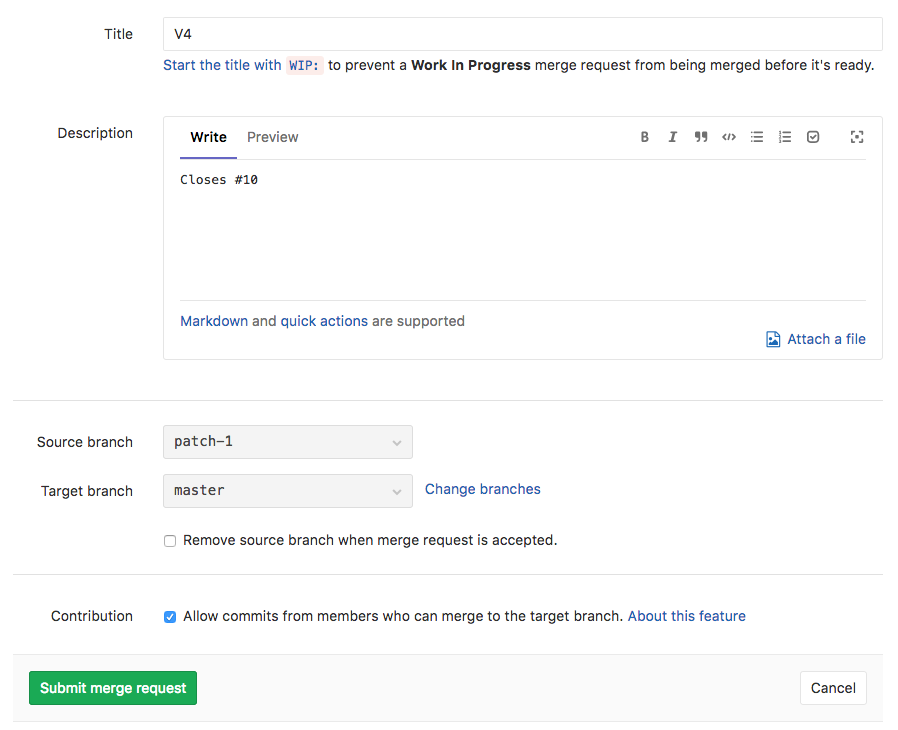
38.6 KB
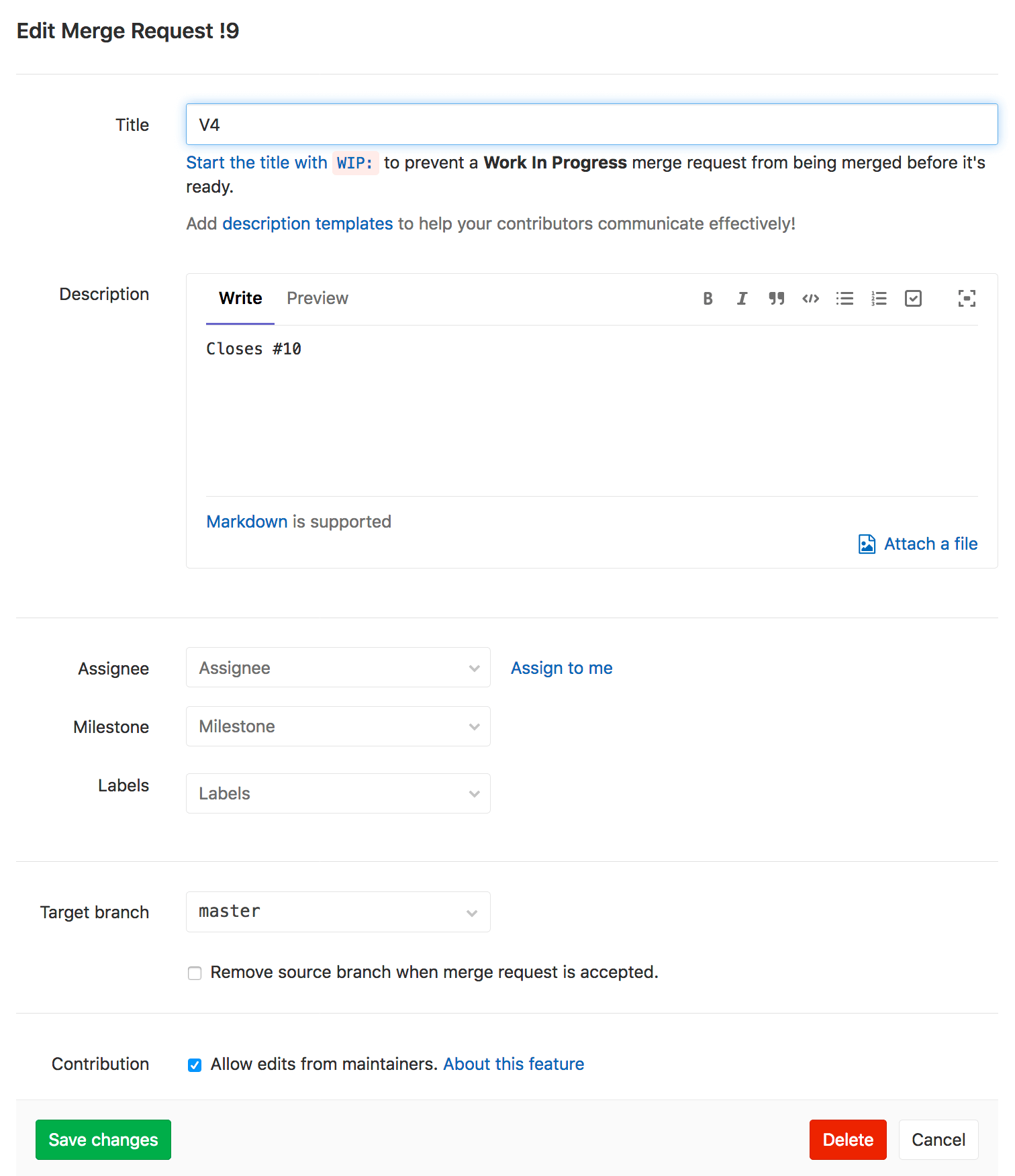
48.1 KB
