Make flags additive and clean up docs
This means that you have to turn on features now instead of disabling them like auth and https. In addition: - Allow multiple options for auth (only password for now). - Combine the install docs since they had many commonalities and - generally simplified them (hopefully not too much). - Move all example configs into docs/examples.
Showing
doc/admin/install/aws.md
已删除
100644 → 0
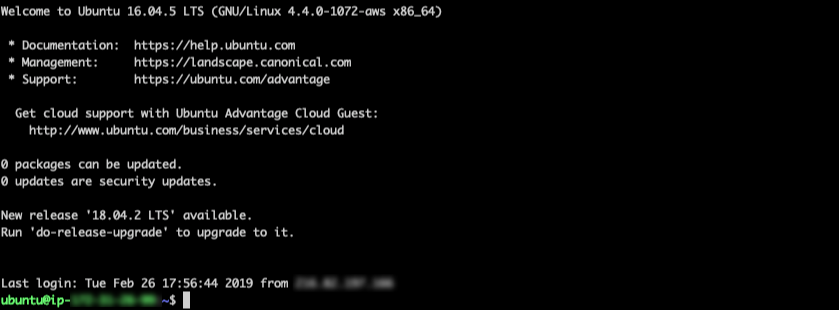
doc/assets/aws_ubuntu.png
已删除
100644 → 0
43.9 KB
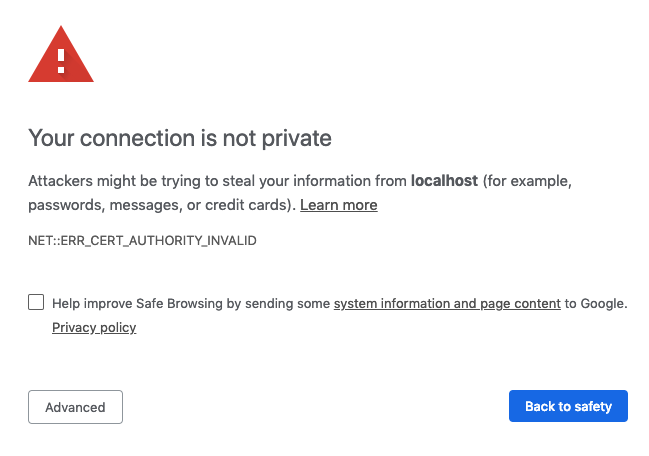
doc/assets/chrome_warning.png
已删除
100644 → 0
30.0 KB
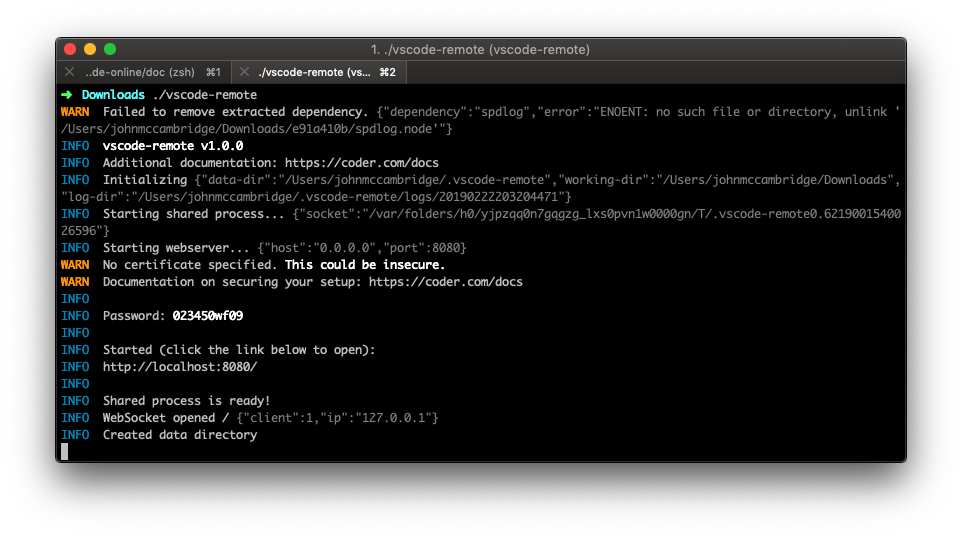
doc/assets/cli.png
已删除
100644 → 0
136.8 KB
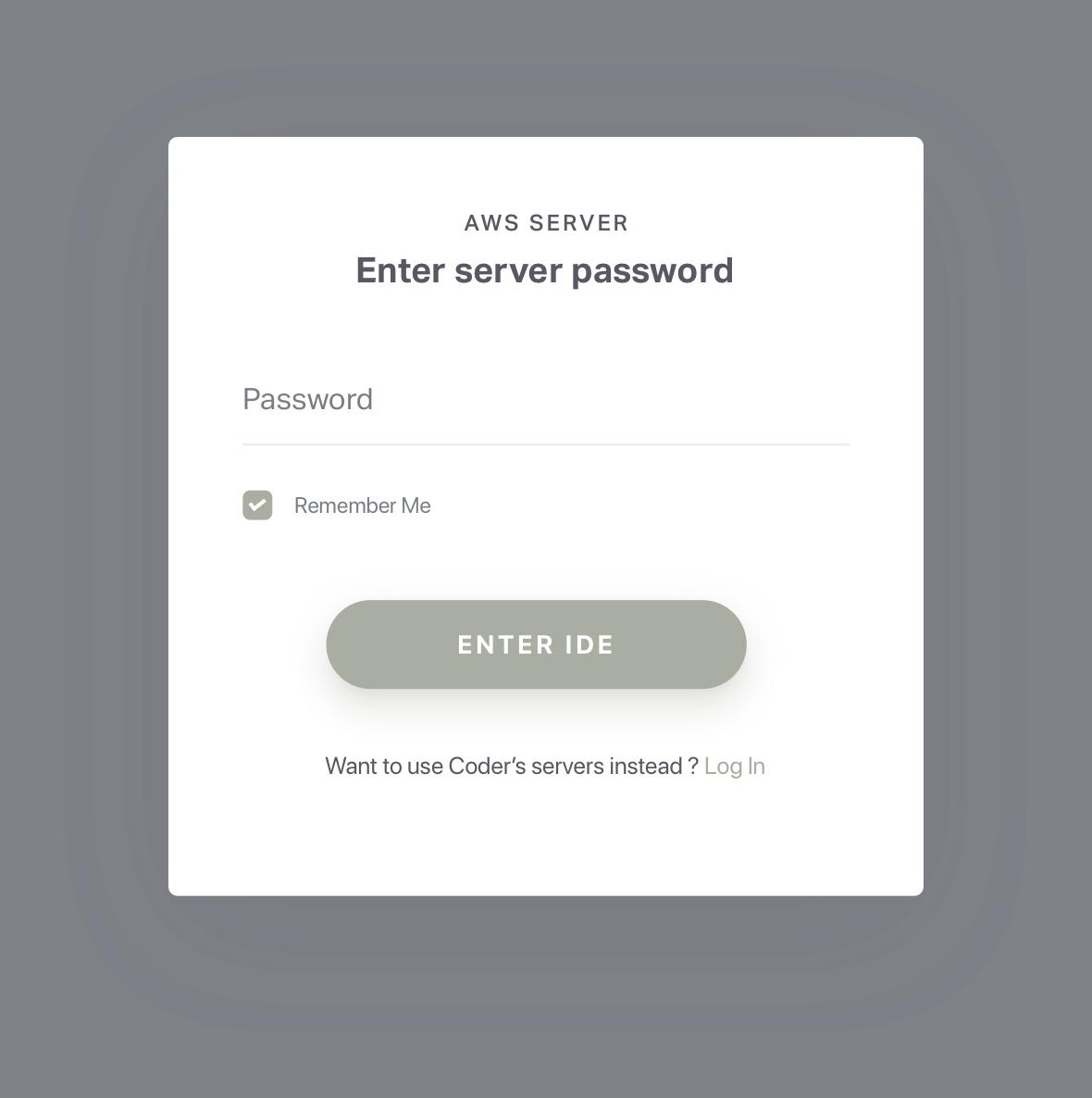
17.5 KB
58.1 KB
doc/deploy.md
0 → 100644
doc/quickstart.md
0 → 100644
doc/security/ssl.md
已删除
100644 → 0
doc/self-hosted/index.md
已删除
100644 → 0